The most expensive technology mistakes I see in small businesses are not the obvious ones. They are the reasonable, well-intentioned decisions that nobody “owns” long enough to think through. An office manager signs up for a cloud tool to solve a real problem. A partner buys a new laptop model because it was on sale. Someone enables a security setting that breaks an app, so they disable it and move on. None of these are reckless. They are normal.
The issue is that “normal” IT decision-making is now a risk model. When your tools, logins, data, backups, and vendor contracts sprawl without a plan, you end up with inefficiency and security exposure. Not good.
Strategy is happening anyway, just not on purpose
Small businesses get told they are too small for leadership-level IT. I disagree. You might be too small for a full-time IT director. You are not too small to need someone thinking about the next 12 to 36 months, because technology decisions compound.
Here is the part most owners miss. When you do not have an IT strategy advisor (often called a virtual CIO), the strategy does not disappear. It gets assigned to whoever is closest to the pain that week. That might be you. It might be an office manager. It might be a well-meaning outsourced IT person who is good at fixing issues but is not being paid to plan. The result is a pile of disconnected “solutions” that are hard to secure, hard to support, and expensive to unwind.
Small businesses are not invisible to attackers either. Verizon’s 2024 DBIR reported that 43% of cyberattacks in 2024 targeted small businesses.1 That is not a reason to panic. It is a reason to stop pretending that ad-hoc tech decisions are harmless.
It gets worse: ad-hoc decisions turn into downtime, rework, and ugly surprises
Most security and reliability failures do not start with a movie-style hack. They start with the boring stuff. An old user account that still works. A cloud app that got connected to email with broad permissions. A backup that exists, but has never been tested. A firewall rule that was opened “temporarily” and stayed that way for two years. This is why I push back when someone tells me, “We just need better security software.” Tools matter, but ownership matters more.
IBM’s SMB analysis found that 60% of small businesses that experienced a data breach in 2023 said the root cause was an ad-hoc or unvetted technology decision, like misconfigured cloud tools or unsupported software, not some sophisticated zero-day exploit.2 That lines up with what I see on the ground. The breach is the headline, but the cause is usually a chain of small decisions that were never reviewed as a system.
Downtime is where this becomes real money. If you are a small business, a “technical issue” is not just an IT problem. It is payroll burning while people wait, clients getting delayed, and leadership getting distracted. Sophos reported that among small businesses hit by ransomware in 2023 – 2024, 58% experienced at least one full business-day of downtime, and 44% said the biggest impact was operational disruption, not the ransom itself.3 A full day is not an inconvenience. It is a financial event.
Now layer in the modern subscription reality. Many businesses I walk into have overlapping tools that do the same thing, and nobody is sure which one is “the real one.” File sharing in three places. Two password managers. Multiple backup approaches, none tested. Licenses that auto-renew annually with price increases, and the only time anyone notices is when the credit card statement hits.
Over a 3 to 5 year window, this is how you end up paying more for less. Not because you are careless, but because there was never a single owner for small business tech planning. Nobody was tasked with asking, “If we buy this, what does it replace? Who administers it? What does it integrate with? How do we recover when it breaks? What is the exit plan if pricing changes?”
Consider a 30-person professional services firm that runs on email, shared files, a practice management system, and a handful of line-of-business apps. They buy a new cloud tool to solve a workflow issue, and they connect it quickly so the team can get back to work. Permissions get granted broadly because it is easier. MFA is inconsistent because some apps support it cleanly and others do not. Backups exist, but the restore process depends on one person knowing where everything lives. Then a major industry incident hits, like the 2024 global Windows outage caused by a faulty update. Firms with no documented continuity plan often lost full business days while they waited for ad-hoc help. Firms with a vCIO-style relationship typically had communication and guidance for recovery, so the response was faster and less chaotic. Same incident, very different outcome.
This is the part that owners find frustrating. They feel like they are already spending plenty on IT. And they usually are, just in the worst way possible: emergency labor, rushed projects, and “surprise” renewals. Gartner’s SMB research found that businesses involving a strategic IT advisor or virtual CIO reduced unplanned technology spending and rework by an average of 25 – 30% over three years compared with reactive peers.4 That is not magic. It is what happens when someone is allowed to think ahead.
The solution: a part-time strategic guide, not another tool
A strategic technology advisor is not a help desk. This role is closer to a part-time IT director whose job is to translate business needs into a technology roadmap, then keep decisions consistent over time.
In practice, that usually means:
- Building a 12 to 36 month technology roadmap, including lifecycle planning for hardware, software, and security controls.
- Setting standards, so you do not have five “special case” laptops and three ways of sharing files.
- Reducing risk by making sure basics are actually implemented, like MFA, account management, backup testing, and incident response planning.
- Reviewing renewals and subscriptions before they auto-renew, so you are paying for what you use.
- Making sure projects have an owner, a budget, and a definition of “done,” so they do not drag on for six months and still fail.
Notice what is missing. There is no magic software. The “solution category” here is a virtual CIO or IT strategy advisor function, paired with the right operational tools, like endpoint detection and response tools, centralized identity and access management, and automated & monitored offsite backups. The advisor makes sure those categories are selected and implemented in a way that matches your business, not a generic checklist.
If you want a deeper dive into one of the highest leverage controls, I wrote a plain-English breakdown of MFA here: The Simple Security Fix Your Small Business Can’t Afford to Ignore. MFA is not “strategy,” but it is a good example of how a small decision can either be done cleanly across the business or done inconsistently and become a future mess.
What can I do right now?
If you do nothing else this week, do these steps. They do not require a big project, and they will immediately clarify where you are exposed.
- Write down who owns technology decisions. Put a name next to it, even if it is you. If the answer is “everyone,” the real answer is “no one.”
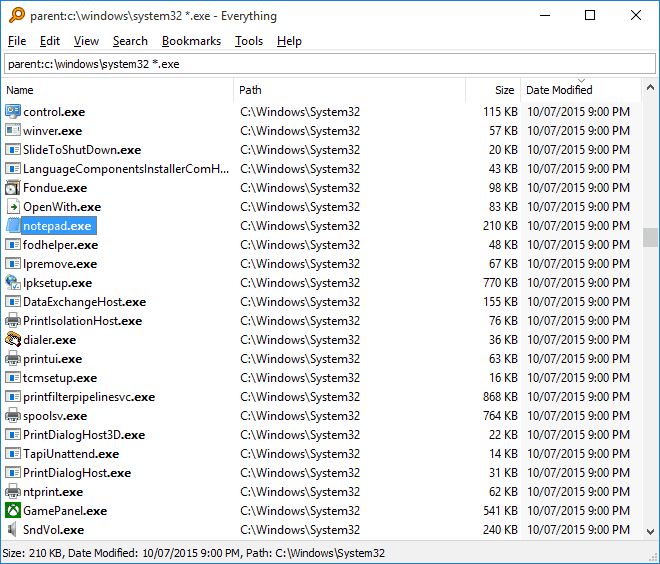
- List every system that can stop your business for a day. Email, files, internet, line-of-business apps, accounting, phones. If you cannot list them in 10 minutes, your environment is already too opaque.
- Pick one critical system and verify MFA is enforced for everyone. Not “available.” Enforced. If exceptions exist, document why.
- Ask one uncomfortable backup question: “When was the last successful full restore test, and how long did it take?” If the answer is “not sure,” treat that as “never.”
- Review renewals for the next 90 days. Subscriptions, security tools, cloud apps, support contracts. Identify anything that auto-renews without a decision. That is where waste hides.
- Create a one-page technology roadmap draft. Three columns: “Must do,” “Should do,” “Not doing.” If you cannot justify a tool or project in one sentence, it probably should not be funded yet.
None of this replaces real IT management, but it forces clarity. Clarity is what stops ad-hoc decisions from turning into expensive surprises.
Have questions, comments, concerns? Get in touch and I’m happy to have a conversation. In the meantime, stay safe out there!
Michael Zull | Founder
Sources
1 Verizon 2024 Data Breach Investigations Report (DBIR), 2024
2 IBM Security, Cost of a Data Breach Report (SMB analysis), 2024
3 Sophos, The State of Ransomware 2024, 2024
4 Gartner, IT Spending and Cost Optimization in SMBs, 2024